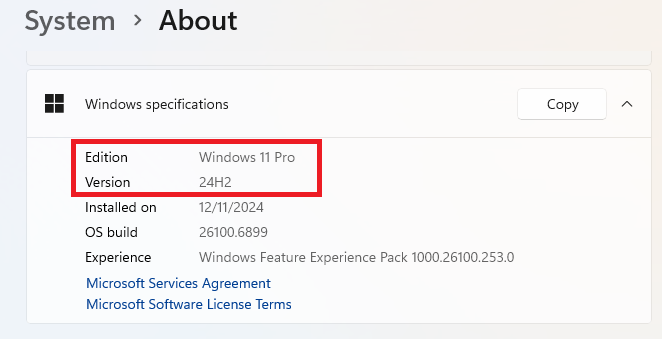
We received a timely phishing email pretending to come from Home Depot. It claimed we’d won a Gorilla Carts dump cart (that’s a sort of four-wheeled wheelbarrow for anyone unfamiliar)—and said it was just one click away.
It wasn’t.
The whole image in the email was clickable, and it hid plenty of surprises underneath.
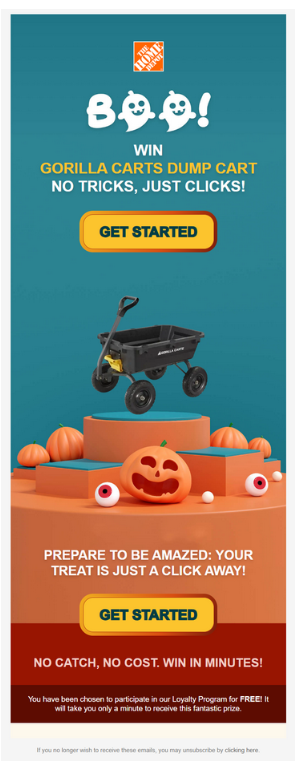
Sender:
The sender email’s domain (yula[.]org) is related neither to Home Depot nor the recipient.
The yula[.]org domain belongs to a Los Angeles high school. The email address or server may be compromised. We have notified them of the incident.
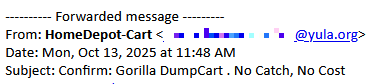
Hidden characters:
Below the main image, we found a block filled with unnecessary Unicode whitespace and control characters (like =E2=80=8C, =C3=82), likely trying to obfuscate its actual content and evade spam filters. The use of zero-width and control Unicode characters is designed to break up strings to confound automated phishing or spam filters, while being invisible to human readers.
Reusing legitimate content:
Below the image we found an order confirmation that appears to be a legitimate transactional message for trading-card storage boxes.
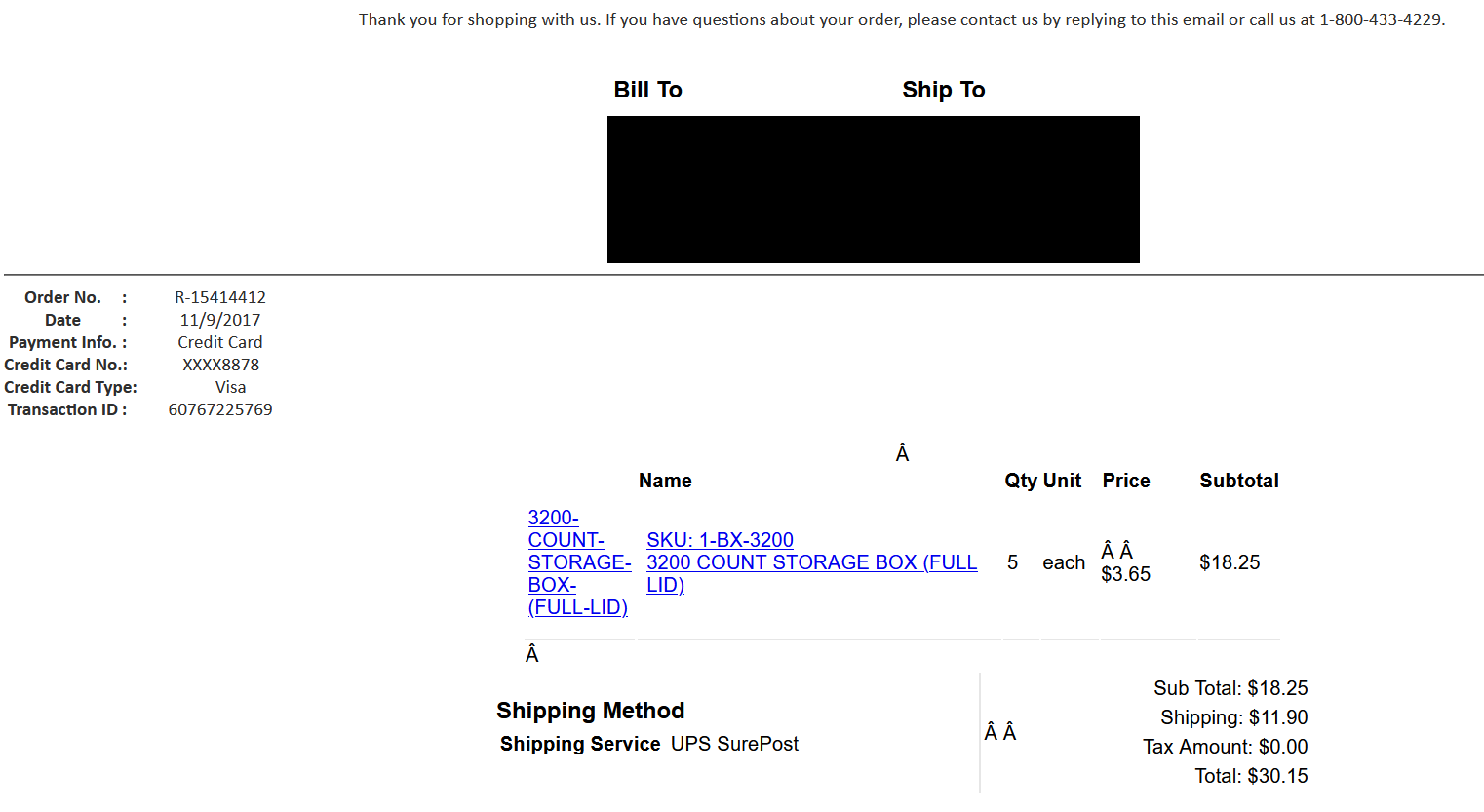
The message seems to be lifted from a chain (there’s a reply asking “When is the expected date of arrival?”), and includes an embedded, very old order confirmation (from 2017) from sales@bcwsupplies[.]com—a real vendor for card supplies.
So, the phisher is reusing benign, historic content (likely harvested from somewhere) to lend legitimacy to the email and to help it sneak past email filters. Many spam and phishing filters (both gateway and client-side) give higher trust scores to emails that look like they’re part of an existing, valid conversation thread or an ongoing business relationship. This is because genuine reply chains are rarely spam or phishing.
Tracking pixel:
We also found a one-pixel image in the mail—likely used to track which emails would be opened. They are almost invisible to the human eye and serve no purpose except to confirm the email was opened and viewed, alerting the attacker that their message landed in a real inbox.
The address of that image was in the subdomain JYEUPPYOXOJNLZRWMXQPCSZWQUFK.soundestlink[.]com. The domain soundestlink[.]com is used by the Omnisend/Soundest email marketing infrastructure for tracking email link clicks, opens, and managing things like “unsubscribe” links. In other words, when someone uses Omnisend to send a campaign, embedded links and tracking pixels in the email often go through this domain so that activity can be logged (clicks, opens, etc.).
Following the trail
That’s a lot of background, so let’s get to the main attraction: the clickable image.
The link leads to https://www.streetsofgold[.]co.uk/wp-content/uploads/2025/05/bluestarguide.html and contains a unique identifier. In many phishing campaigns, each recipient gets a unique tracking token in the URL, so attackers know exactly whose link was clicked and when. This helps them track engagement, validate their target list, and potentially personalize follow-ups or sell ‘confirmed-open’ addresses.
The streetsofgold[.]co.uk WordPress instance hasn’t been updated since 2023 and is highly likely compromised. The HTML file on that site redirects visitors to bluestarguide[.]com, which immediately forwards to outsourcedserver[.]com, adding more tracking parameters. It took a bit of tinkering and a VPN (set to Los Angeles) to follow the chain of redirects, but I finally ended up at the landing page.
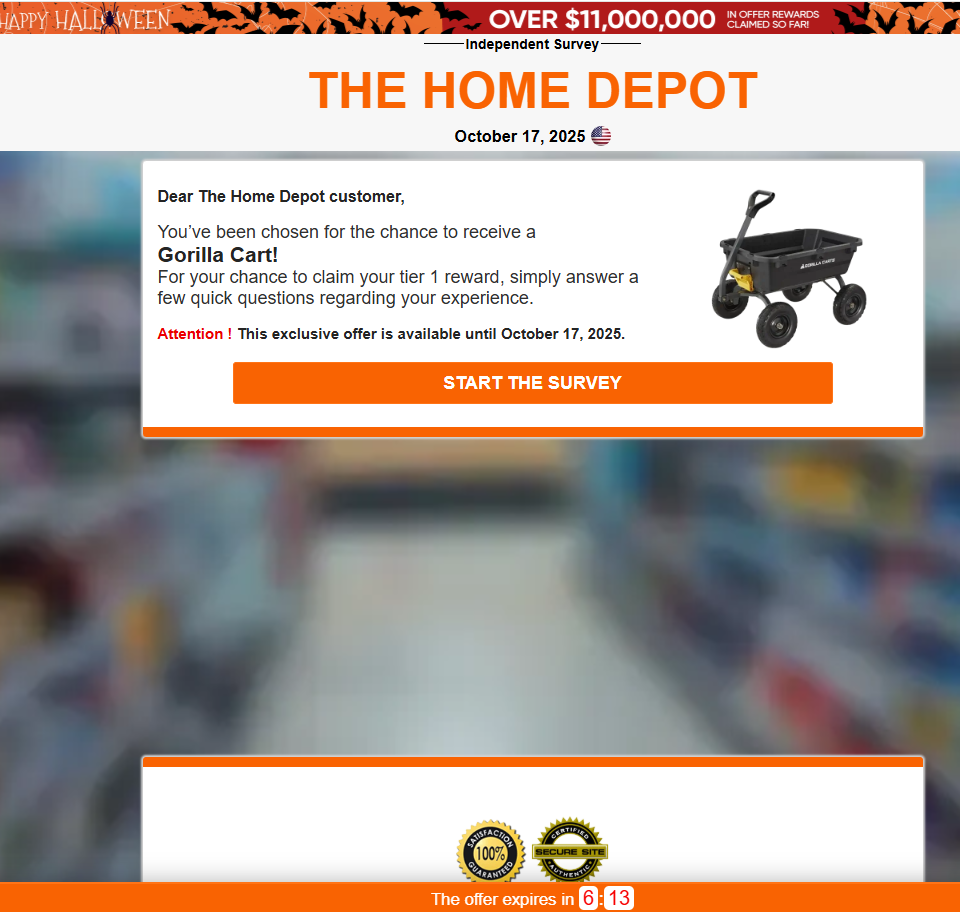
Of course, urgency was applied so visitors don’t take the time to think things through. The site said the offer was only valid for a few more minutes. The “one-click” promise quickly turned into a survey—answering basic questions about my age and gender, I was finally allowed to “order” my free Gorilla Cart.
The fake reward
But no surprise here, now they wanted shipping details.
Wait… what? A small processing fee?!
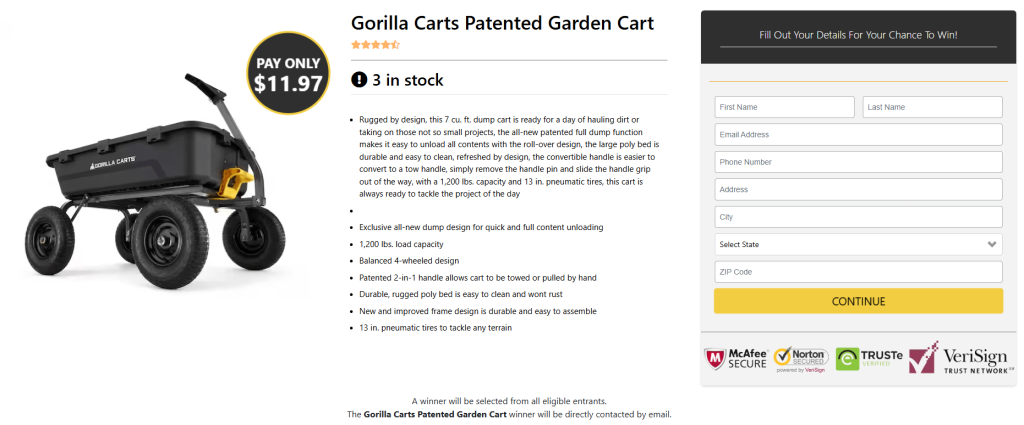
This is as far as I got. After filling out the details, I kept getting this error.
“Something went wrong with the request, Please try again.”
The backend showed that the submitted data was handled locally at /prize/ajax.php?method=new_prospect on prizewheelhub[.]com with no apparent forwarding address. Likely, after “collecting” the personal info, the backend:
- stores it for later use in phishing or identity theft,
- possibly emails it to a criminal/“affiliate” scammer, and/or
- asks for credit card or payment details in a follow-up.
We’re guessing all of the above.
Tips to stay safe
This campaign demonstrates that phishing is often an adaptive, multi-stage process, combining technical and psychological tricks. The best defense is a mix of technical protection and human vigilance.
The best way to stay safe is to be aware of these scams, and look out for red flags:
- Don’t click on links in unsolicited emails.
- Always check the sender’s address against the legitimate one you would expect.
- Double-check the website’s address before entering any information.
- Use an up-to-date real-time anti-malware solution with a web protection component.
- Don’t fill out personal details on unfamiliar websites.
- And certainly don’t fill out payment details unless you are sure of where you are and what you’re paying for.
IOCs
During this campaign we found and blocked these domains:
www.streetsofgold[.]co.uk (compromised WordPress website)
bluestarguide[.]com (redirector)
outsourcedserver[.]com (fingerprint and redirect)
sweepscraze[.]online
prizewheelhub[.]com
techstp[.]com
Other domains we found associated with bluestarguide[.]com
substantialweb[.]com
quelingwaters[.]com
myredirectservices[.]com
prizetide[.]online