Online crime of all kinds is deplorable, but romance scammers and sextortionists who target the most vulnerable victims are among the worst. Now, there’s likely a place for 260 of them in jail, thanks to international law enforcement.
Interpol’s Operation Contender 3.0 targeted alleged criminals from several countries across Africa. It arrested 260 people and captured 1,235 electronic devices. Investigators linked 1,463 victims to the scams, and said their losses amounted to around $2.8 million.
The images from Interpol’s press release tell just as lurid a story as the numbers do. In one, over 30 phones lie on a table, each with a different case. These were the devices that the scammers likely used to carry out their crimes, which focused on romance scams and extortion.
Criminals lured victims with fake online identities built from stolen photos and forged documents, then exploited victims through romance scams that demanded bogus courier or customs fees. Others ran sextortion schemes, secretly recording explicit video chats to extort money.
What to watch for
Romance scams are all too familiar to those in the know, but still catch out plenty of lonely people looking for affection online. A criminal half a world away will get to know a victim, often beginning the relationship via an ‘accidental’ text message, or via a dating site or social media. A fake social media account, usually with a stolen photo, lends them credibility. They will gradually get to know the victim, luring them into what seems like a romantic relationship. If you’re talking to someone who claims to be in the military and therefore unable to travel, be very wary. This is a common scam tactic.
Eventually the request for money will come, in some form or other. In some scams, it’ll be a recommendation to invest in a fraudulent investment scheme (this used to be called ‘pig butchering’ but now Interpol prefers the more humane term ‘romance baiting’).
In other variations of the scam, there will be a plan to visit the victim – except, of course, there’s some financial hurdle that the perpetrator must overcome before they can travel. If the victim sends the money, the requests will keep coming, always with another excuse for why they can’t make the trip just yet.
Talking with someone you’ve never met who’s asking for financial help with a medical emergency, or to solve a legal or business issue? Think twice before sending the funds. Then think a third time. Then don’t do it.
A loneliness epidemic
In an era where people are increasingly lonely, romance scams are a surprisingly effective tactic. Americans lost $1.2 billion to romance scammers last year, with medium losses hitting $2,000.
The extortion side of things is even more horrid. People aren’t just lonely these days; they’re lusty. That leads to many people doing things online with strangers that they shouldn’t, including sharing intimate images or videos of themselves. Once a criminal has those assets, they can use them to extort the victims by threatening to send the material to their friends, family, and professional contacts.
Romance scams and other forms of financial fraud can come from anywhere, including in your own country. But Africa does seem to be a hotbed for it. Last year’s Interpol Africa Cyberthreat Assessment Report found that cybercrime accounted for 30% of all reported crime in Western and Eastern Africa. Criminals engage in many kinds of digital crime, according to the report, including business email compromise and banking malware, but online scams are especially popular—as is digital sextortion and harassment.
Interpol arrested eight people a year ago in Nigeria and Côte d’Ivoire for financial fraud including romance scams as part of its Contender 2.0 operation. And in 2022, it dismantled a South African gang for swindling companies, but also suspected it of being involved in romance scams.
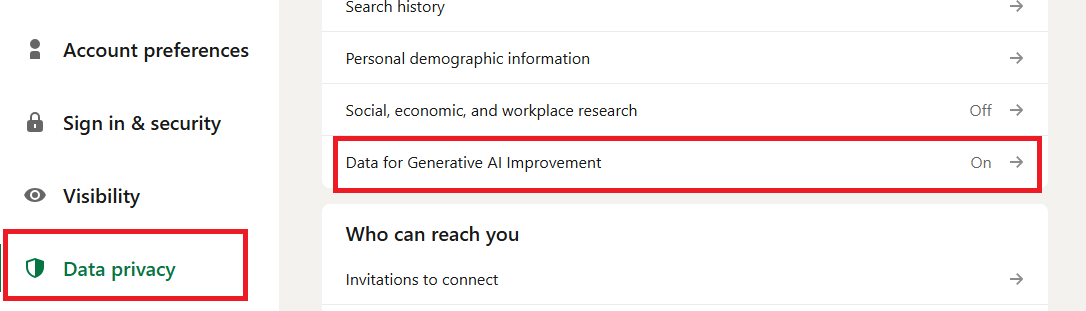
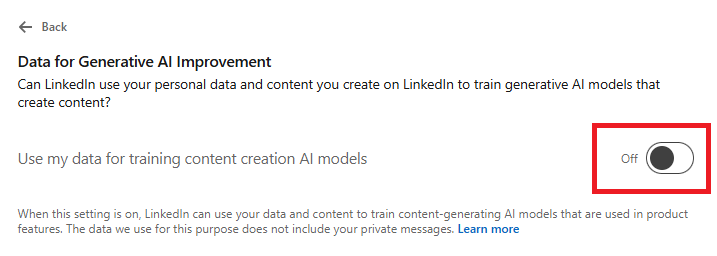
We don’t just report on scams—we help detect them
Cybersecurity risks should never spread beyond a headline. If something looks dodgy to you, check if it’s a scam using Malwarebytes Scam Guard, a feature of our mobile protection products. Submit a screenshot, paste suspicious content, or share a text or phone number, and we’ll tell you if it’s a scam or legit. Download Malwarebytes Mobile Security for iOS or Android and try it today!