Early September, a security researcher uncovered a new vulnerability in Magento, an open-source e-commerce platform used by thousands of online retailers, and its commercial counterpart Adobe Commerce. It sounds like something straight out of a horror movie: SessionReaper. Behind the cinematic name hides a very real and very dangerous remote code execution flaw, tracked as CVE-2025-54236. It allows attackers to hijack live customer sessions—and, in some setups, even take full control of the server that runs the store.
SessionReaper lives in a part of Magento that handles communication between the store and other services. The bug stems from improper input validation and unsafe handling of serialized data. In plain terms, Magento sometimes trusts data that no web application ever should. This lets an attacker trick the system into accepting a specially crafted “session” file as a legitimate user login—no password required.
What they can do with that login depends on how the store is configured, but researchers at SecPod warn:
“Successful exploitation of SessionReaper can lead to several severe consequences, including security feature bypass, customer account takeover, data theft, fraudulent orders, and potentially remote code execution.”
Session-stealers like this one mean a compromised store can quietly expose a shopper’s personal details, order information, or payment data to attackers. In some cases, criminals inject “skimmer” code that harvests card details as you type them in or reroutes you to phishing sites designed to look like legitimate checkouts.
A patch for the vulnerability was released on September 9, but six weeks later, roughly 62% of Magento stores reportedly remain unpatched. After someone published a proof-of-concept (PoC), cybercriminals quickly built working exploits and attacks are now spreading fast. So, while SessionReaper isn’t malware a shopper can “catch” directly, it can turn even trusted stores into possible data-theft traps until the site owners patch.
Researchers at Sansec, whose sensors monitor e-commerce attacks worldwide, report seeing more than 250 Magento stores compromised within 24 hours of the exploit code going public.
How consumers can stay safe
Web store owners should patch their Magento sites immediately. Unfortunately, regular shoppers have almost no way to tell whether a store is still vulnerable or already secured.
From a consumer’s point of view, SessionReaper is another reminder that even trusted stores can quietly become unsafe between page loads. When a platform as widespread as Magento is under active attack, the best defense often lies outside the store itself.
- Watch out for odd behavior on a site or missing valid HTTPS, and don’t enter payment or personal data if something seems suspicious.
- Where possible, opt for checkout options that use third-party gateways (like PayPal), as they’re isolated from the store’s servers.
- Report suspicious e-commerce behavior to the site operator or your payment provider straight away.
- Shop on reputable sites whenever you can, or check the reviews and reputation of any new sellers before buying.
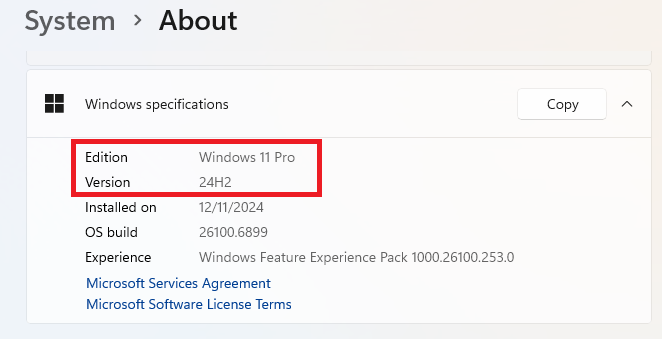
- Make sure your operating system, browser, and anti-malware software are up to date to protect against the latest threats.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.