One of my favorite Forbes correspondents recently wrote about receiving several fake copyright-infringement notices from X.
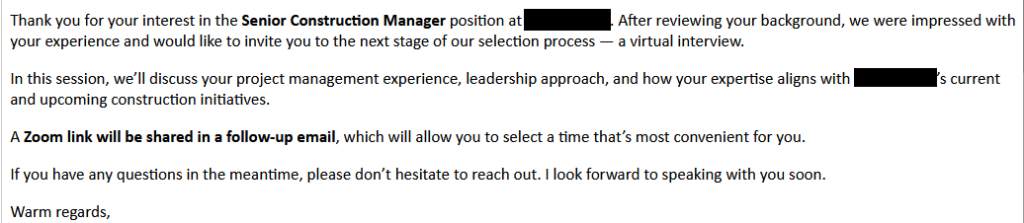
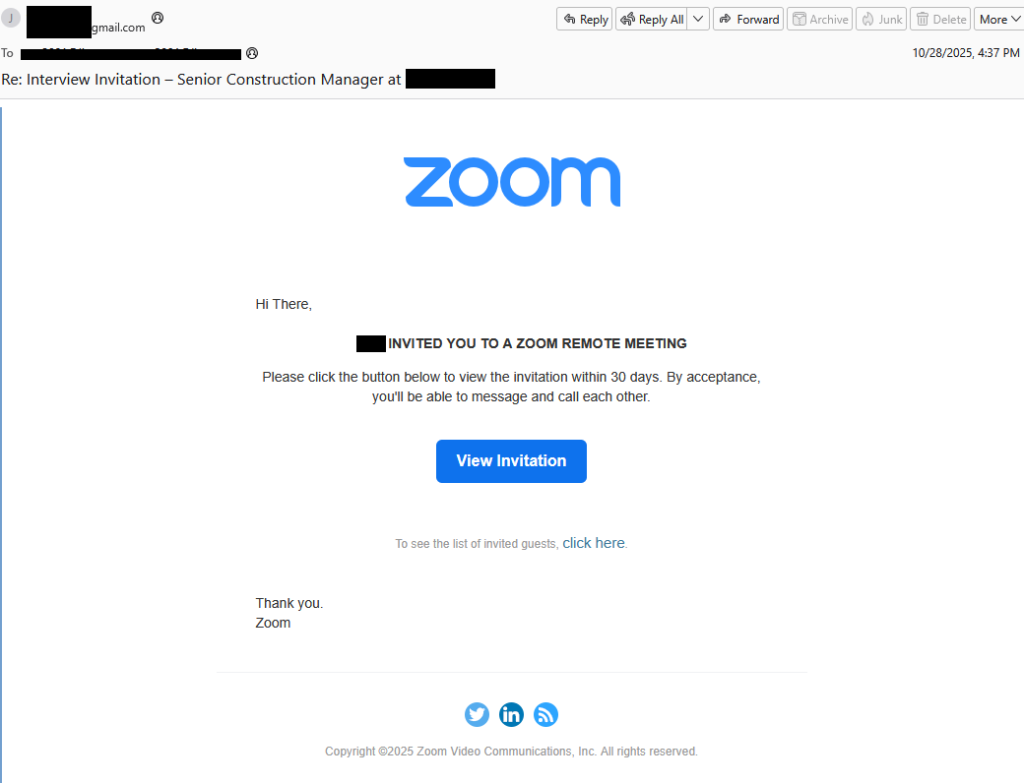
Let’s suppose you get an email claiming it’s from X, warning:
“We’ve received a DMCA notice regarding your account.”
Chances are, you’ll be wondering what you did wrong. DMCA (Digital Millennium Copyright Act) notices are legal requests about copyrighted content, so it makes sense that many users would worry they broke the rules and feel eager to read the warning.
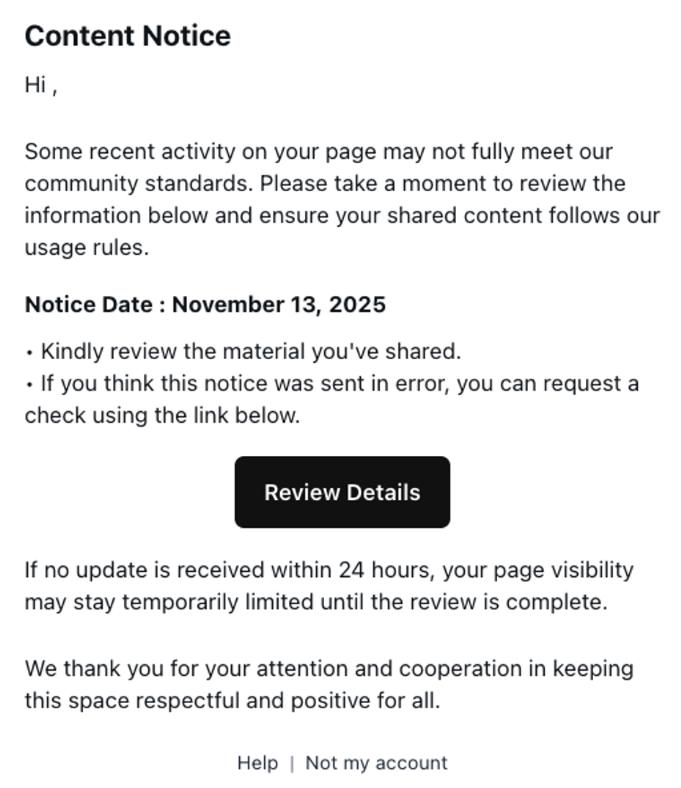
“Some recent activity on your page may not fully meet our community standards. Please take a moment to review the information below and ensure your shared content follow our usage rules.
Notice Date : {day received}”
- Kindly review the material You’ve shared.
- If you think this notice was sent in error, you can request a check using the link below.
Review Details {button}
If no update is received within 24 hours, your page visibility may stay temporarily limited until the review is complete.
We thank you for your attention and cooperation in keeping this space respectful and positive for all.”
As usual, the scammers add some extra pressure by claiming your account may be hidden or limited if you don’t act within 24 hours.
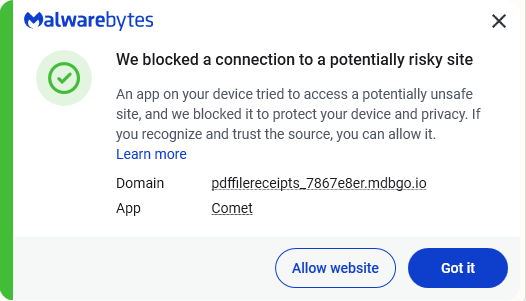
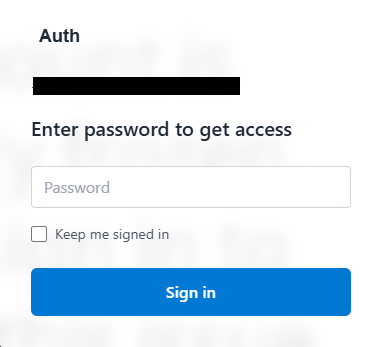
But the “Review Details” button doesn’t lead to anything on X. It does look a lot like the X login page, but it’s fake.
Any username and password typed there go straight to the hackers—which could leave you with a compromised account.
How to keep your X account safe
Having your X account stolen can be a major pain for you, your followers, and your reputation (especially if you’re in the cybersecurity field). So here are some tips to keep it safe:
- Make sure 2FA is turned on. We wrote an article about how to do this back when it was still called Twitter.
- When entering a username and password, or any type of sensitive information, check whether the URL in the address bar matches what you expect.
- Use a password manager. It won’t enter your details on a fake site.
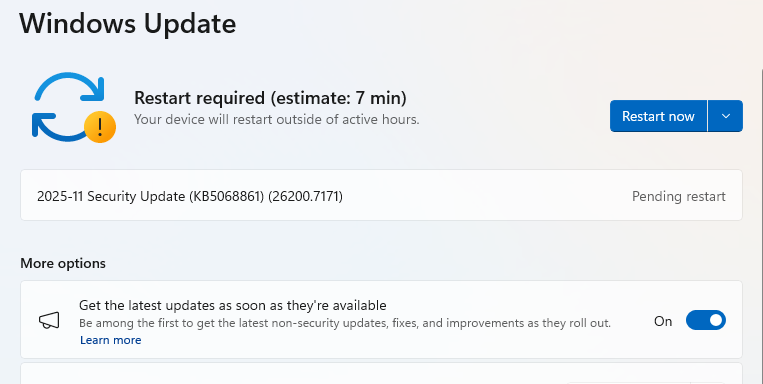
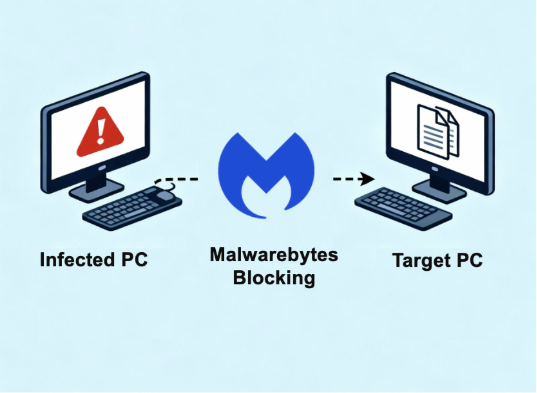
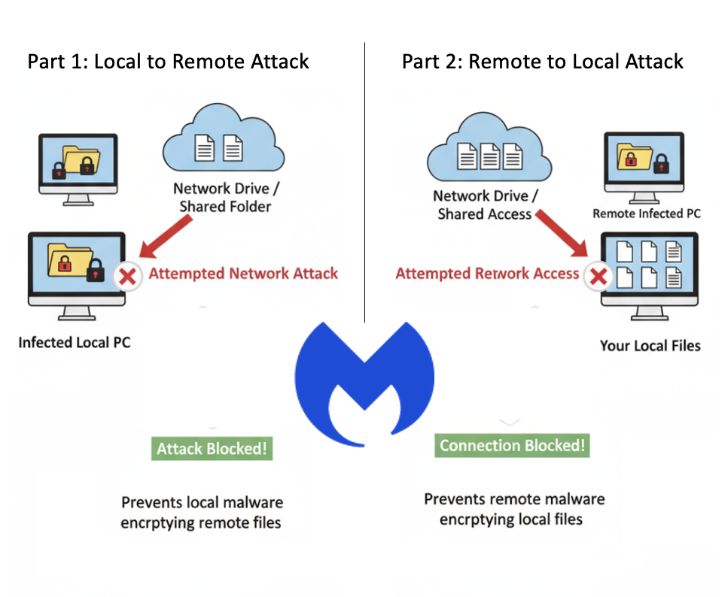
- Use an up-to-date real-time anti malware solution with a web protection component.
- Don’t click on links in unsolicited emails and check with the sender through another channel first.
- A real DMCA notice from X will include a full copy of the reporter’s complaint, including contact details, plus instructions for filing a counter-notice.
Pro tip: You can upload suspicious messages of any kind to Malwarebytes Scam Guard. It will tell you whether it’s likely to be a scam and advise you what to do.
If you suspect your account may be compromised:
- Change your password.
- Make sure your email account associated with the account is secure.
- Revoke connections to third-party applications.
- Update your password in the third-party applications that you trust.
- Contact Support if you can’t log in after trying the above.
Here are the full instructions from X for users who believe their accounts have been compromised.
We don’t just report on scams—we help detect them
Cybersecurity risks should never spread beyond a headline. If something looks dodgy to you, check if it’s a scam using Malwarebytes Scam Guard, a feature of our mobile protection products. Submit a screenshot, paste suspicious content, or share a text or phone number, and we’ll tell you if it’s a scam or legit. Download Malwarebytes Mobile Security for iOS or Android and try it today!

![Be careful responding to unexpected job interviews 6 Malwarebytes blocks meetingzs[.]com](https://www.malwarebytes.com/wp-content/uploads/sites/2/2025/11/meetingzscomblock.png)

![Phishing emails disguised as spam filter alerts are stealing logins 18 Malwarebytes Browser Guard blocks the subdomain of mdbgo[.]io](https://www.malwarebytes.com/wp-content/uploads/sites/2/2025/11/mdbgoioblock.png)